NAC-ABE Design » History » Revision 5
« Previous |
Revision 5/13
(diff)
| Next »
Suravi Regmi, 11/24/2025 07:51 PM
NAC-ABE Design¶
What NAC-ABE Provides¶
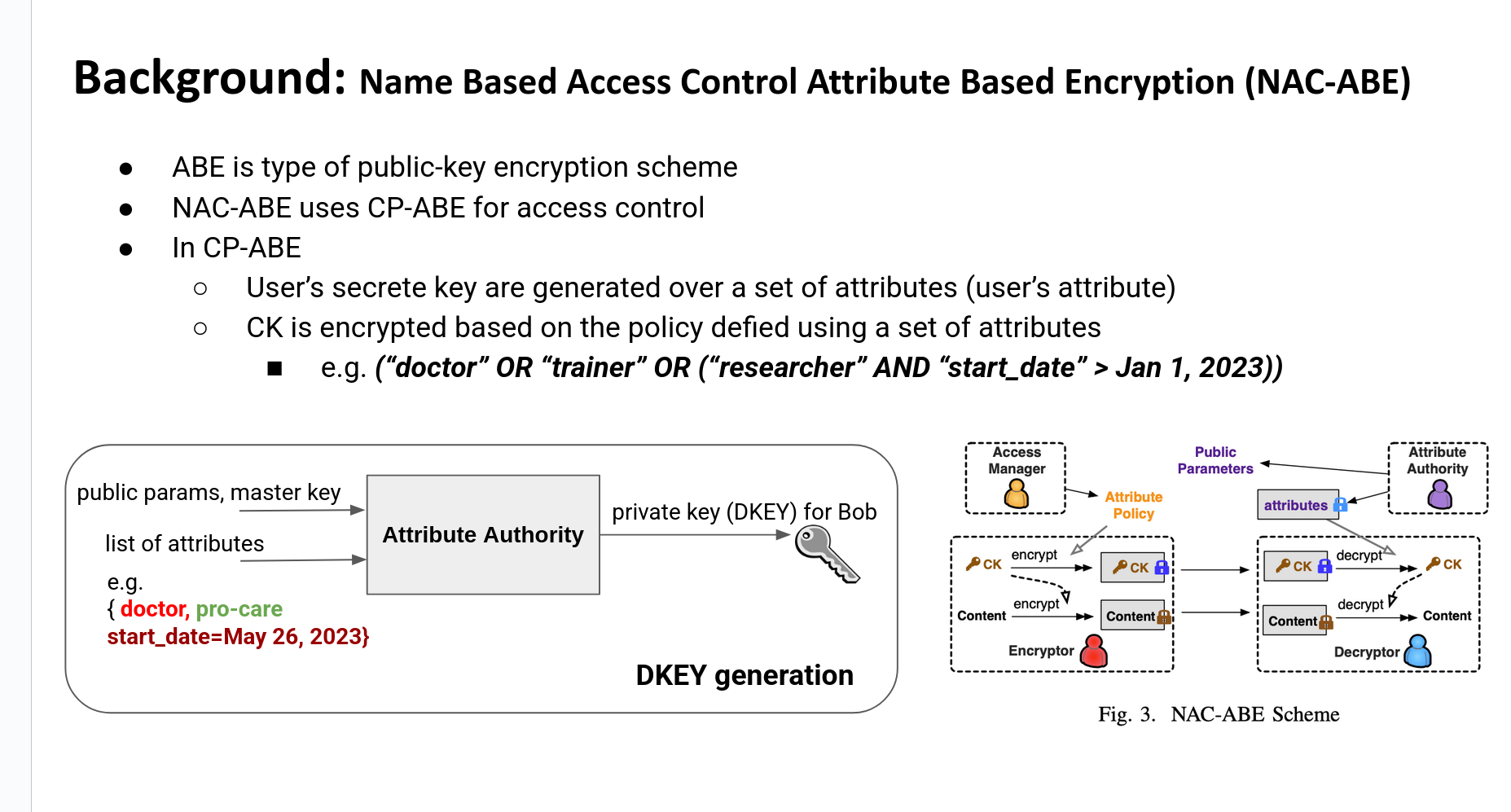
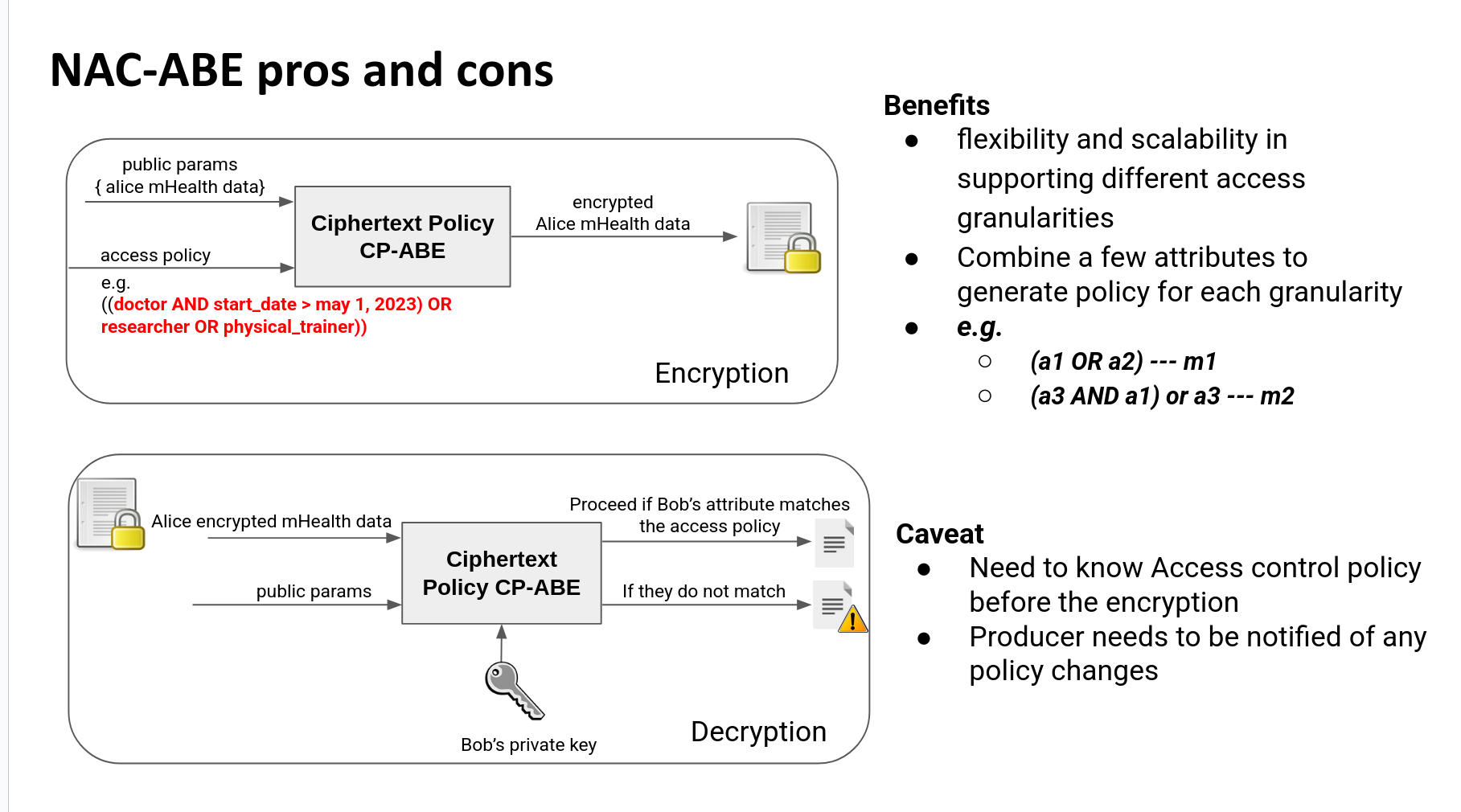
NAC-ABE implements name-based access control using two layers:
- Symmetric encryption of data using Content Key (CK).
- ABE encryption of CK using AA-issued public parameters and consumer policies.
Data is encrypted with a CK, and the CK itself is encrypted under ABE so that only authorized consumers holding a matching Decryption Key (DKEY) can recover it.
The Attribute Authority (AA) publishes public parameters and issues DKEYs, while NAC-ABE producers generate CKs and encrypted data using these parameters.
This removes the need for any online authorization server during data fetch and enables cryptographically enforced access control at the packet level.
Why mGuard Uses KP-ABE¶
A KP-ABE policy defines which identities can receive a Decryption Key (DKEY) and which data attributes that DKEY authorizes them to decrypt. Each policy includes:
- A policy-id, which uniquely identifies the policy.
- A list of requester-names, representing the NDN identities that will receive the DKEY generated from this policy.
- One or more attribute-filters, typically expressed as namespace prefixes. These prefixes determine which encrypted Content Keys (CKs) the resulting DKEY can decrypt.
Policies are evaluated using exact prefix matching. If the attribute attached by the producer during CK generation starts with a prefix listed in an allow-filter, a DKEY created from that policy will successfully decrypt the CK.
No role-based or device-level semantics are required; access control is driven entirely by namespace prefixes embedded within attributes.
KP-ABE supports stream-specific semantics and flexible downstream authorization.
In KP-ABE, the producer assigns an attribute string to each Content Key (CK). The consumer receives a DKEY that contains a policy, usually expressed as one or more namespace prefixes. Decryption succeeds when:
- policy_prefix is a prefix of attribute_string
This creates a simple, deterministic Matching Rule:
The producer attaches attributes to CKs.
The consumer holds a DKEY containing a prefix-based policy.
Authorization is validated locally through prefix comparison.
T he producer never evaluates policies and never needs access to DKEYs. All authorization takes place on the consumer side using the policy embedded in the DKEY.
Certificates¶
NAC-ABE uses two distinct certificates, each serving a different purpose in the trust and encryption pipeline.
Stream Certificate¶
The stream certificate defines the namespace and identity under which CKs and encrypted data are published. NAC-ABE derives CK names from this certificate:
/<stream-identity>/CK/<random>/ENC-BY/<attributes>/seg=i
Encrypted data packets are also named under the same identity prefix. This ensures that each stream's data and CKs are isolated and validated using the stream's trust chain.
Attribute Authority (AA) Certificate¶
The AA certificate anchors the ABE trust domain. It is used to validate:
Public Parameters (PUBPARAMS)
AA KEY packets
Any ABE-related metadata
The AA certificate ensures that only authenticated parameters are used for CK generation and that consumers can trust the DKEYs they receive.
3. ABE Encryption of CK (Black Box Description)¶
When the producer encrypts one data chunk:
- Producer calls:
- Output:
- a fresh symmetric CK
- CK segments encrypted with KP-ABE (using AA public parameters)
- Producer encrypts the data payload with CK.
- Producer embeds the CK name inside the encrypted data.
- Producer publishes:
- CK segments
- encrypted data segments
The consumer later:
- fetches CK segments,
- decrypts CK using its DKEY,
- decrypts the encrypted data.
The producer treats ABE internals as a complete black box.
4. Certificates in NAC-ABE (Updated mGuard Behavior)¶
4.1 Stream Identity Certificate¶
The stream’s certificate is used by NAC-ABE for:
a) Naming CKs
Updated mGuard naming:
//CK//ENC-BY//seg=i
This scopes CKs to each stream.
Different streams produce CKs under different prefixes.
b) Naming encrypted data
//
This maintains per-stream isolation.
c) Signing and trust schema validation
All CK and encrypted data packets are signed according to the stream’s identity chain.
4.2 AA Certificate¶
The AA certificate is used as the trusted root of ABE.
It enables the producer and consumer to:
- Validate AA Public Parameters (PUBPARAMS).
- Validate AA KEY packets.
- Determine ABE type from PUBPARAMS (KP-ABE vs CP-ABE).
- Run
kpContentKeyGen()(needs verified public params).
The AA certificate defines the mathematical ABE domain; the stream certificate defines the namespace and signing authority for CK and data packets.
5. End-to-End Flow (Producer → Repo → Consumer)¶
Content Key (CK)¶
A CK is the symmetric key used to encrypt data.
CK rotation frequency determines how precisely access control can be enforced.
A user can only decrypt data encrypted with CKs they are authorized to received.
Content Key (CK)¶
A CK is the symmetric key used to encrypt data. CK rotation frequency determines access-control precision. A user can only decrypt data encrypted with CKs they are authorized for.
CK Granularity¶
- Second-level: maximum precision, very high overhead
- Minute-level: balanced precision vs cost
- Hour-level: minimal overhead, coarse control Granularity determines access-control precision and system cost.
CK vs Access-Control Granularity¶
CK granularity must be equal to or finer than the access-control granularity.
| Access Control ↓ / CK → | second | minute | hour |
|---|---|---|---|
| second | ✔️ | ❌ | ❌ |
| minute | ✔️ | ✔️ | ❌ |
| hour | ✔️ | ✔️ | ✔️ |
Rule: CK rotation cannot be coarser than the authorization window.
CK Reuse Tradeoffs¶
High reuse (minute/hour): fewer CK packets, low cost; coarse control.
Low reuse (second): fine-grain control; many CKs, high overhead.
Implementation Note¶
Most encryption overhead is CK generation, not data encryption; finer CK granularity increases load.
Updated by Suravi Regmi 5 months ago · 13 revisions